 They say history repeats itself, and this has once again proven to be true in the area of network and computer security.
They say history repeats itself, and this has once again proven to be true in the area of network and computer security.
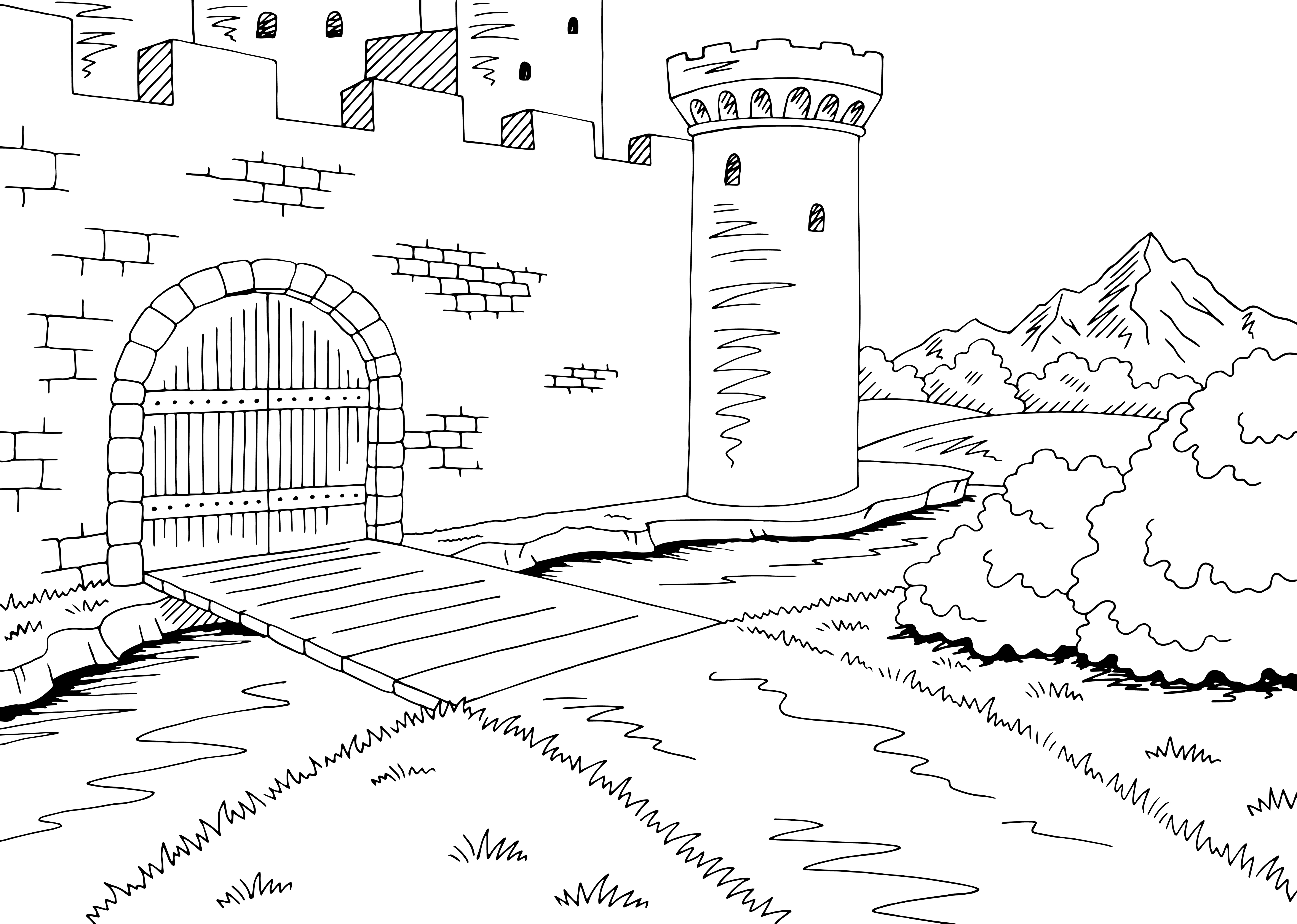
In the past, wise kings would build stone castles with solid wooden and steel doors only accessible after crossing a wide moat. After vetting, guests would be permitted inside the castle gates. Once inside, visitors may be subject to search, potential detention and still more locked doors and gates prior to reaching their final objectives.
This methodology is mirrored in today’s best security environments.
By deploying cloud security products you are able to build a virtual moat around your network. Cloud security enables you to block attacks before they ever reach the network edge by examining the source of the data to determine if it poses a threat. Once at the edge of your network, data will need to pass through the firewall / castle gates to enter the network. Current firewalls, often rebranded as Security Appliances or Next Generation Firewalls, perform enhanced inspection of traffic to minimize the threat of attack or malicious content from entering the network.
Inside the network, behavioral analytic tools inspect data traffic once again to determine if there is a need to block or quarantine files and processes. Upon reaching their final destination of computer or server, files and processes are screened yet again by anti-virus/malware or more vigorous application inspection programs to ensure that only pre-approved files and processes run.
Whether you’re the king of the castle, a network administrator or a chief security officer, these protective measures will only prevent malicious activity when everyone continues to operate in a cautious and conscientious manner; your environment is only as secure as your most careless citizen/user. User awareness training is critical in ensuring that the defenses put in place are not circumvented when someone doesn’t follow protocol. End-user training is critical to maintaining a secure computing environment and must include topics such as password storage, phishing, social engineering and other end-user rampart-preserving points of contact.
If you’re concerned with the state of your castle’s security or would like learn more about protecting your network or educating your users, contact Keno Kozie’s team of security consults at [email protected]. Our network warriors are ready to assist in the defense of your network.
